The mechanism is called harvest now, decrypt later — HNDL. An adversary with sufficient resources intercepts and stores encrypted communications today. The data is currently unreadable. When a cryptographically relevant quantum computer exists, the archived data is decrypted.
The Global Risk Institute’s 2026 Quantum Threat Timeline Report assesses a cryptographically relevant quantum computer as “quite possible within ten years, likely within fifteen.” In February 2026, Google publicly called on governments and enterprises to begin post-quantum migration immediately, citing its own March 2026 research showing that elliptic curve cryptography — the foundation of most current secure communications — could be broken with approximately 500,000 physical qubits. That figure is significantly lower than previous estimates.
Medical records, legal communications, government intelligence, and corporate intellectual property encrypted in 2025 become accessible in 2035. The threat is not future. The exposure is present.
The standards exist. The migration has not started.
In August 2024, NIST finalised three post-quantum cryptographic algorithms — FIPS 203, 204, and 205 — following an eight-year global evaluation process involving 82 candidate algorithms from 25 countries. The standards are published. They are freely available. They are technically mature.
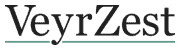
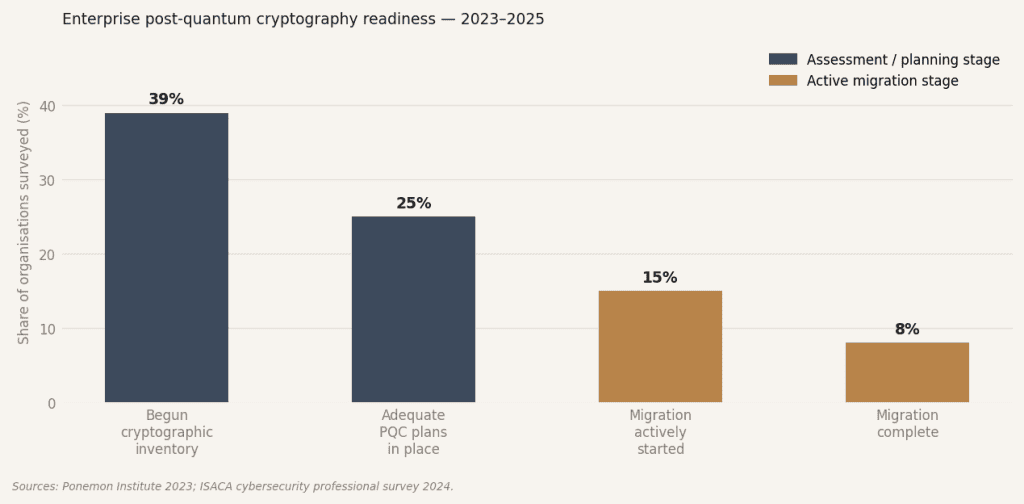
A full post-quantum cryptographic migration takes two to five years for most organisations. The first step is a cryptographic inventory: identifying every system, vendor, and hardware component that relies on the algorithms now known to be vulnerable. A 2023 Ponemon Institute survey found that 61% of organisations had not begun that inventory. ISACA reported that fewer than 25% of cybersecurity professionals considered their organisation’s post-quantum plans adequate.
The governance failure
The gap between “standards exist” and “organisations are migrating” is not primarily a technical failure. It is a governance failure. The risk is technical. The decision to act is organisational. The two have not been connected at board level in most enterprises.
Google Cloud expects to complete post-quantum cryptography across its infrastructure by the end of 2026. Microsoft made PQC APIs generally available across its platform in 2025. The infrastructure providers are moving. The enterprises that use them, largely, are not.
The historical precedent is NotPetya in 2017, which cost Maersk alone an estimated $300 million and demonstrated, conclusively, that cryptographic infrastructure risk is consistently underestimated until it materialises. The difference is that NotPetya was unexpected. The quantum threat is documented, quantified, and timetabled. The organisations that fail to migrate will not be able to claim they were not warned.
“The quantum threat to encryption is not coming. It is already here — in every intercepted packet sitting in a foreign intelligence archive, waiting for hardware that the industry itself says is ten years away.”
SOURCES
— NIST — FIPS 203, 204, 205 post-quantum cryptographic standards, August 2024
— Global Risk Institute — Quantum Threat Timeline Report 2026
— Google Security Blog — post-quantum migration, February 2026
— Ponemon Institute — 2023 cryptographic inventory survey
— ISACA — post-quantum readiness survey
— World Economic Forum — quantum security for leaders, February 2026— BCG — How Quantum Computing Will Upend Cybersecurity, November 2025